Diferencia entre revisiones de «IdM / FreeIPA»
| Línea 410: | Línea 410: | ||
== Creación de grupo y usuario en IdM == | == Creación de grupo y usuario en IdM == | ||
Crear un grupo en IdM | === Crear un grupo en IdM === | ||
<syntaxhighlight lang="bash"> | <syntaxhighlight lang="bash"> | ||
| Línea 422: | Línea 422: | ||
</syntaxhighlight> | </syntaxhighlight> | ||
Crear usuario | === Crear usuario === | ||
<syntaxhighlight lang="bash"> | <syntaxhighlight lang="bash"> | ||
[root@nodo1 ~]# ipa user-add jadmin --first=Juan --last=Admin --password | [root@nodo1 ~]# ipa user-add jadmin --first=Juan --last=Admin --password | ||
| Línea 450: | Línea 450: | ||
</syntaxhighlight> | </syntaxhighlight> | ||
Añadir usuario a un grupo | === Añadir usuario a un grupo === | ||
<syntaxhighlight lang="bash"> | <syntaxhighlight lang="bash"> | ||
[root@nodo1 ~]# ipa group-add-member admins-linux --users=jadmin | [root@nodo1 ~]# ipa group-add-member admins-linux --users=jadmin | ||
| Línea 462: | Línea 462: | ||
</syntaxhighlight> | </syntaxhighlight> | ||
Verificaciones | === Verificaciones === | ||
Grupos: | Grupos: | ||
Revisión del 09:52 3 feb 2026
Identity Management (IdM / FreeIPA)
Introducción
Identity Management (IdM), basado en FreeIPA, es la solución de Red Hat para la gestión centralizada de identidades. IdM integra varios servicios en una única plataforma:
- LDAP (389 Directory Server)
- Kerberos
- DNS
- Certificados (Dogtag CA)
- Gestión de usuarios, grupos y políticas
En RHEL 9, IdM es la solución recomendada y soportada oficialmente para servicios de directorio.
Requisitos previos
- IP estática configurada
- Hostname con FQDN correcto
- Resolución de nombre funcional
- Sincronización horaria activa (NTP)
- Acceso a repositorios oficiales de RHEL
Ejemplo:
192.168.1.81 nodo1.jagfloriano.com nodo1
Preparación del sistema
Comprobar hostname y FQDN:
[root@nodo1 ~]# hostname
nodo1
[root@nodo1 ~]# hostname -f
nodo1.jagfloriano.com
[root@nodo1 ~]# hostnamectl
Static hostname: nodo1
Icon name: computer-vm
Chassis: vm 🖴
Machine ID: 20ff935e15e14490a6e182f1a7979010
Boot ID: daaaf7f2b9104421820d256e95a711c3
Virtualization: oracle
Operating System: Red Hat Enterprise Linux 9.7 (Plow)
CPE OS Name: cpe:/o:redhat:enterprise_linux:9::baseos
Kernel: Linux 5.14.0-570.12.1.el9_6.x86_64
Architecture: x86-64
Firmware Version: VirtualBox
Comprobar resolución de nombre:
[root@nodo1 ~]# getent hosts nodo1
fe80::a00:27ff:fef3:3c51 nodo1
Verificar sincronización horaria:
[root@nodo1 ~]# timedatectl
Local time: Tue 2026-02-03 09:19:15 CET
Universal time: Tue 2026-02-03 08:19:15 UTC
RTC time: Tue 2026-02-03 08:19:15
Time zone: Europe/Madrid (CET, +0100)
System clock synchronized: yes
NTP service: active
RTC in local TZ: no
Instalación de paquetes IdM
Instalar el grupo de paquetes del servidor IdM:
dnf install -y ipa-server ipa-server-dns
Verificar instalación:
[root@nodo1 ~]# rpm -qa | grep ipa
python3-iniparse-0.4-45.el9.noarch
libipa_hbac-2.9.7-4.el9_7.1.x86_64
sssd-ipa-2.9.7-4.el9_7.1.x86_64
device-mapper-multipath-libs-0.8.7-39.el9_7.1.x86_64
device-mapper-multipath-0.8.7-39.el9_7.1.x86_64
ipa-client-common-4.12.2-22.el9_7.1.noarch
python3-libipa_hbac-2.9.7-4.el9_7.1.x86_64
ipa-selinux-4.12.2-22.el9_7.1.noarch
ipa-common-4.12.2-22.el9_7.1.noarch
ipa-healthcheck-core-0.16-9.el9.noarch
redhat-logos-ipa-90.5-1.el9_6.1.noarch
ipa-server-common-4.12.2-22.el9_7.1.noarch
python3-ipalib-4.12.2-22.el9_7.1.noarch
python3-ipaclient-4.12.2-22.el9_7.1.noarch
ipa-client-4.12.2-22.el9_7.1.x86_64
python3-ipaserver-4.12.2-22.el9_7.1.noarch
ipa-server-4.12.2-22.el9_7.1.x86_64
ipa-server-dns-4.12.2-22.el9_7.1.noarch
Configuración inicial del servidor IdM
La configuración inicial se realiza mediante el asistente `ipa-server-install`.
Ejecutar el instalador:
ipa-server-install
Durante el asistente se solicitará:
- Nombre de dominio (ej: jagfloriano.com)
- Realm Kerberos (ej: JAGFLORIANO.COM)
- Contraseña del usuario admin
- Configuración del DNS integrado
- Reenvíos DNS (forwarders)
- Confirmación de instalación
Valores recomendados:
- Usar DNS integrado
- Configurar al menos un DNS forwarder
- Mantener el realm en mayúsculas
[root@nodo1 ~]# ipa-server-install
The log file for this installation can be found in /var/log/ipaserver-install.log
==============================================================================
This program will set up the IPA Server.
Version 4.12.2
This includes:
* Configure a stand-alone CA (dogtag) for certificate management
* Configure the NTP client (chronyd)
* Create and configure an instance of Directory Server
* Create and configure a Kerberos Key Distribution Center (KDC)
* Configure Apache (httpd)
* Configure SID generation
* Configure the KDC to enable PKINIT
To accept the default shown in brackets, press the Enter key.
Do you want to configure integrated DNS (BIND)? [no]:
Enter the fully qualified domain name of the computer
on which you're setting up server software. Using the form
<hostname>.<domainname>
Example: master.example.com
Server host name [nodo1.jagfloriano.com]:
The domain name has been determined based on the host name.
Please confirm the domain name [jagfloriano.com]:
The kerberos protocol requires a Realm name to be defined.
This is typically the domain name converted to uppercase.
Please provide a realm name [JAGFLORIANO.COM]:
Certain directory server operations require an administrative user.
This user is referred to as the Directory Manager and has full access
to the Directory for system management tasks and will be added to the
instance of directory server created for IPA.
The password must be at least 8 characters long.
Directory Manager password:
Password (confirm):
The IPA server requires an administrative user, named 'admin'.
This user is a regular system account used for IPA server administration.
IPA admin password:
Password (confirm):
Trust is configured but no NetBIOS domain name found, setting it now.
Enter the NetBIOS name for the IPA domain.
Only up to 15 uppercase ASCII letters, digits and dashes are allowed.
Example: EXAMPLE.
NetBIOS domain name [JAGFLORIANO]:
Do you want to configure chrony with NTP server or pool address? [no]:
The IPA Master Server will be configured with:
Hostname: nodo1.jagfloriano.com
IP address(es): 192.168.1.81
Domain name: jagfloriano.com
Realm name: JAGFLORIANO.COM
The CA will be configured with:
Subject DN: CN=Certificate Authority,O=JAGFLORIANO.COM
Subject base: O=JAGFLORIANO.COM
Chaining: self-signed
Continue to configure the system with these values? [no]: yes
The following operations may take some minutes to complete.
Please wait until the prompt is returned.
Disabled p11-kit-proxy
Synchronizing time
No SRV records of NTP servers found and no NTP server or pool address was provided.
Using default chrony configuration.
Attempting to sync time with chronyc.
Time synchronization was successful.
Configuring directory server (dirsrv). Estimated time: 30 seconds
Configuring client side components
This program will set up IPA client.
Version 4.12.2
Using existing certificate '/etc/ipa/ca.crt'.
Client hostname: nodo1.jagfloriano.com
Realm: JAGFLORIANO.COM
DNS Domain: jagfloriano.com
IPA Server: nodo1.jagfloriano.com
BaseDN: dc=jagfloriano,dc=com
Configured /etc/sssd/sssd.conf
Systemwide CA database updated.
Adding SSH public key from /etc/ssh/ssh_host_ed25519_key.pub
Adding SSH public key from /etc/ssh/ssh_host_ecdsa_key.pub
Adding SSH public key from /etc/ssh/ssh_host_rsa_key.pub
Could not update DNS SSHFP records.
SSSD enabled
Configured /etc/openldap/ldap.conf
Configured /etc/ssh/ssh_config
Configured /etc/ssh/sshd_config.d/04-ipa.conf
Configuring jagfloriano.com as NIS domain.
Client configuration complete.
The ipa-client-install command was successful
unable to resolve host name nodo1.jagfloriano.com. to IP address, ipa-ca DNS record will be incomplete
unable to resolve host name nodo1.jagfloriano.com. to IP address, ipa-ca DNS record will be incomplete
Please add records in this file to your DNS system: /tmp/ipa.system.records.h3qbc22f.db
==============================================================================
Setup complete
Next steps:
1. You must make sure these network ports are open:
TCP Ports:
* 80, 443: HTTP/HTTPS
* 389, 636: LDAP/LDAPS
* 88, 464: kerberos
* 53: bind
UDP Ports:
* 88, 464: kerberos
* 53: bind
* 123: ntp
2. You can now obtain a kerberos ticket using the command: 'kinit admin'
This ticket will allow you to use the IPA tools (e.g., ipa user-add)
and the web user interface.
Be sure to back up the CA certificates stored in /root/cacert.p12
These files are required to create replicas. The password for these
files is the Directory Manager password
The ipa-server-install command was successful
Arranque y verificación
Comprobar el estado de los servicios de IdM:
[root@nodo1 ~]# ipactl status
Directory Service: RUNNING
krb5kdc Service: RUNNING
kadmin Service: RUNNING
httpd Service: RUNNING
ipa-custodia Service: RUNNING
pki-tomcatd Service: RUNNING
ipa-otpd Service: RUNNING
ipa: INFO: The ipactl command was successful
Todos los servicios deben aparecer en estado *RUNNING*.
Comprobar acceso administrativo obteniendo un ticket Kerberos:
[root@nodo1 ~]# kinit admin
Password for admin@JAGFLORIANO.COM:
Verificar que el ticket Kerberos se ha obtenido correctamente:
[root@nodo1 ~]# klist
Ticket cache: KCM:0
Default principal: admin@JAGFLORIANO.COM
Valid starting Expires Service principal
02/03/2026 09:34:32 02/04/2026 09:23:23 krbtgt/JAGFLORIANO.COM@JAGFLORIANO.COM
Ver información global del dominio IdM:
[root@nodo1 ~]# ipa config-show
Maximum username length: 32
Maximum hostname length: 64
Home directory base: /home
Default shell: /bin/sh
Default users group: ipausers
Default e-mail domain: jagfloriano.com
Search time limit: 2
Search size limit: 100
User search fields: uid,givenname,sn,telephonenumber,ou,title
Group search fields: cn,description
Enable migration mode: False
Certificate Subject base: O=JAGFLORIANO.COM
Password Expiration Notification (days): 4
Password plugin features: AllowNThash, KDC:Disable Last Success
SELinux user map order: guest_u:s0$xguest_u:s0$user_u:s0$staff_u:s0-s0:c0.c1023$sysadm_u:s0-s0:c0.c1023$unconfined_u:s0-s0:c0.c1023
Default SELinux user: unconfined_u:s0-s0:c0.c1023
Default PAC types: MS-PAC, nfs:NONE
IPA masters: nodo1.jagfloriano.com
IPA master capable of PKINIT: nodo1.jagfloriano.com
IPA CA servers: nodo1.jagfloriano.com
IPA CA renewal master: nodo1.jagfloriano.com
Este comando muestra, entre otros datos:
- Dominio IPA
- Realm Kerberos
- Servidores configurados
Ver dominios asociados al realm Kerberos:
[root@nodo1 ~]# ipa realmdomains-show
Domain: jagfloriano.com
Ver información del servidor IdM:
[root@nodo1 ~]# ipa server-show nodo1.jagfloriano.com
Server name: nodo1.jagfloriano.com
Managed suffixes: domain, ca
Min domain level: 1
Max domain level: 1
Enabled server roles: CA server, IPA master
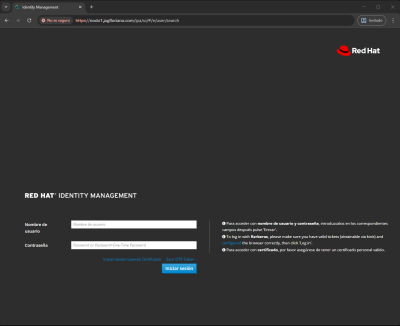
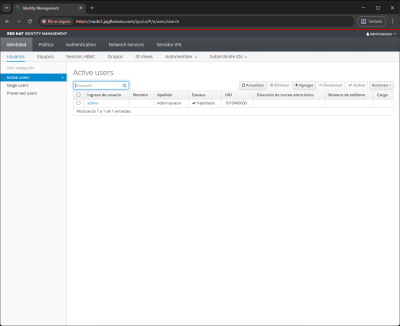
Acceso web
IdM proporciona una interfaz web de administración.
https://nodo1.jagfloriano.com
Acceder con el usuario admin.
|
|
Firewall
Durante la instalación, IdM configura automáticamente el firewall. Puertos principales utilizados:
- 389/TCP (LDAP)
- 636/TCP (LDAPS)
- 88/TCP y UDP (Kerberos)
- 464/TCP y UDP (Kerberos)
- 443/TCP (Web UI)
- 53/TCP y UDP (DNS, si se habilita)
Resultado de la instalación
Al finalizar la instalación:
- IdM está operativo
- LDAP, Kerberos y DNS funcionan de forma integrada
- El sistema está listo para crear usuarios y grupos
- Los clientes pueden unirse al dominio
Creación de grupo y usuario en IdM
Crear un grupo en IdM
[root@nodo1 ~]# ipa group-add admins-linux --desc="Grupo de administradores Linux"
--------------------------
Added group "admins-linux"
--------------------------
Group name: admins-linux
Description: Grupo de administradores Linux
GID: 1010400003
Crear usuario
[root@nodo1 ~]# ipa user-add jadmin --first=Juan --last=Admin --password
Password:
Enter Password again to verify:
-------------------
Added user "jadmin"
-------------------
User login: jadmin
First name: Juan
Last name: Admin
Full name: Juan Admin
Display name: Juan Admin
Initials: JA
Home directory: /home/jadmin
GECOS: Juan Admin
Login shell: /bin/sh
Principal name: jadmin@JAGFLORIANO.COM
Principal alias: jadmin@JAGFLORIANO.COM
User password expiration: 20260203085841Z
Email address: jadmin@jagfloriano.com
UID: 1010400004
GID: 1010400004
Password: True
Member of groups: ipausers
Kerberos keys available: True
Añadir usuario a un grupo
[root@nodo1 ~]# ipa group-add-member admins-linux --users=jadmin
Group name: admins-linux
Description: Grupo de administradores Linux
GID: 1010400003
Member users: jadmin
-------------------------
Number of members added 1
-------------------------
Verificaciones
Grupos:
[root@nodo1 ~]# ipa group-show admins-linux
Group name: admins-linux
Description: Grupo de administradores Linux
GID: 1010400003
Member users: jadmin
Usuarios:
[root@nodo1 ~]# ipa group-show admins-linux
Group name: admins-linux
Description: Grupo de administradores Linux
GID: 1010400003
Member users: jadmin
[root@nodo1 ~]# ipa user-show jadmin
User login: jadmin
First name: Juan
Last name: Admin
Home directory: /home/jadmin
Login shell: /bin/sh
Principal name: jadmin@JAGFLORIANO.COM
Principal alias: jadmin@JAGFLORIANO.COM
Email address: jadmin@jagfloriano.com
UID: 1010400004
GID: 1010400004
Account disabled: False
Password: True
Member of groups: admins-linux, ipausers
Kerberos keys available: True
Confirmar que el usuario lo ve el sistema:
[root@nodo1 ~]# id jadmin
uid=1010400004(jadmin) gid=1010400004(jadmin) groups=1010400004(jadmin),1010400003(admins-linux)
Gestionar privilegios con IdM (sudo)
En este ejemplo se configura una regla de sudo en IdM para que los miembros del grupo admins-linux puedan ejecutar el comando systemctl restart NetworkManager como root y **sin introducir contraseña**.
[root@nodo1 ~]# sudo -l -U jadmin
User jadmin is not allowed to run sudo on nodo1.
Configuración del cliente IdM para sudo
Antes de definir reglas en IdM, el cliente debe estar configurado para consumir reglas sudo mediante SSSD.
Configurar authselect
[root@nodo1 ~]# authselect select sssd with-sudo with-mkhomedir --force
Backup stored at /var/lib/authselect/backups/2026-02-03-09-24-26.779SBz
Profile "sssd" was selected.
The following nsswitch maps are overwritten by the profile:
- passwd
- group
- netgroup
- automount
- services
- sudoers
Make sure that SSSD service is configured and enabled. See SSSD documentation for more information.
- with-mkhomedir is selected, make sure pam_oddjob_mkhomedir module
is present and oddjobd service is enabled and active
- systemctl enable --now oddjobd.service
Reiniciar servicios y limpiar la caché:
[root@nodo1 ~]# systemctl restart sssd
[root@nodo1 ~]# sssctl cache-expire --everything
Configuración de SSSD
El fichero /etc/sssd/sssd.conf debe contener una configuración similar
a la siguiente:
[domain/jagfloriano.com]
id_provider = ipa
auth_provider = ipa
access_provider = ipa
chpass_provider = ipa
sudo_provider = ipa
ipa_server_mode = True
ipa_server = nodo1.jagfloriano.com
ipa_domain = jagfloriano.com
ipa_hostname = nodo1.jagfloriano.com
cache_credentials = True
ldap_tls_cacert = /etc/ipa/ca.crt
krb5_store_password_if_offline = True
[sssd]
services = nss, pam, ifp, ssh, sudo
domains = jagfloriano.com
[nss]
homedir_substring = /home
memcache_timeout = 600
[pam]
[sudo]
[autofs]
[ssh]
[pac]
[ifp]
allowed_uids = ipaapi, root
[session_recording]
Permisos correctos del fichero:
chmod 600 /etc/sssd/sssd.conf
Nota importante:
En sistemas que actúan como servidor IdM (ipa_server_mode = True) es recomendable definir explícitamente:
sudo_provider = ipa
Ejemplo práctico: sudo para reiniciar NetworkManager
En este ejemplo se permite que los miembros del grupo admins-linux
ejecuten el comando:
/usr/bin/systemctl restart NetworkManager como root y sin contraseña en el host nodo1.jagfloriano.com.
Crear el comando sudo
[root@nodo1 ~]# ipa sudocmd-add "/usr/bin/systemctl restart NetworkManager"
--------------------------------------------------------------
Added Sudo Command "/usr/bin/systemctl restart NetworkManager"
--------------------------------------------------------------
Sudo Command: /usr/bin/systemctl restart NetworkManager
Crear la regla de sudo
[root@nodo1 ~]# ipa sudorule-add restart-networkmanager --desc="Permitir reiniciar NetworkManager"
----------------------------------------
Added Sudo Rule "restart-networkmanager"
----------------------------------------
Rule name: restart-networkmanager
Description: Permitir reiniciar NetworkManager
Enabled: True
2.3 Asignar el grupo de usuarios
[root@nodo1 ~]# ipa sudorule-add-user restart-networkmanager --groups=admins-linux
Rule name: restart-networkmanager
Description: Permitir reiniciar NetworkManager
Enabled: True
User Groups: admins-linux
-------------------------
Number of members added 1
-------------------------
Asignar el host
Si no existe el hostgroup all, es obligatorio asignar el host explícitamente a la regla sudo.
[root@nodo1 ~]# ipa sudorule-add-host restart-networkmanager --hosts=nodo1.jagfloriano.com
Rule name: restart-networkmanager
Description: Permitir reiniciar NetworkManager
Enabled: True
User Groups: admins-linux
Hosts: nodo1.jagfloriano.com
Sudo Allow Commands: /usr/bin/systemctl restart NetworkManager
Sudo Option: !authenticate
-------------------------
Number of members added 1
-------------------------
Permitir el comando
[root@nodo1 ~]# ipa sudorule-add-allow-command restart-networkmanager --sudocmds="/usr/bin/systemctl restart NetworkManager"
Rule name: restart-networkmanager
Description: Permitir reiniciar NetworkManager
Enabled: True
User Groups: admins-linux
External host: all
Sudo Allow Commands: /usr/bin/systemctl restart NetworkManager
-------------------------
Number of members added 1
-------------------------
Configurar ejecución sin contraseña
[root@nodo1 ~]# ipa sudorule-add-option restart-networkmanager --sudooption='!authenticate'
------------------------------------------------------------------
Added option "!authenticate" to Sudo Rule "restart-networkmanager"
------------------------------------------------------------------
Rule name: restart-networkmanager
Description: Permitir reiniciar NetworkManager
Enabled: True
User Groups: admins-linux
External host: all
Sudo Allow Commands: /usr/bin/systemctl restart NetworkManager
Sudo Option: !authenticate
Verificación
Limpiar la caché del cliente:
sssctl cache-expire --everything
systemctl restart sssd
Comprobar permisos:
[root@nodo1 ~]# sudo -l -U jadmin
Matching Defaults entries for jadmin on nodo1:
!visiblepw, always_set_home, match_group_by_gid, always_query_group_plugin, env_reset, env_keep="COLORS DISPLAY HOSTNAME HISTSIZE KDEDIR LS_COLORS", env_keep+="MAIL PS1 PS2 QTDIR USERNAME LANG LC_ADDRESS LC_CTYPE", env_keep+="LC_COLLATE LC_IDENTIFICATION LC_MEASUREMENT LC_MESSAGES",
env_keep+="LC_MONETARY LC_NAME LC_NUMERIC LC_PAPER LC_TELEPHONE", env_keep+="LC_TIME LC_ALL LANGUAGE LINGUAS _XKB_CHARSET XAUTHORITY", secure_path=/sbin\:/bin\:/usr/sbin\:/usr/bin
User jadmin may run the following commands on nodo1:
(root) NOPASSWD: /usr/bin/systemctl restart NetworkManager
Prueba final:
[root@nodo1 ~]# su - jadmin
Creating home directory for jadmin.
Last login: Tue Feb 3 10:17:18 CET 2026 on pts/0
[jadmin@nodo1 ~]$ sudo systemctl restart NetworkManager
[jadmin@nodo1 ~]$
Errores comunes y notas técnicas
- No ejecutar
authselect select sssd with-sudoen el cliente - No definir
sudo_provider = ipaen servidores IdM - Crear sudo rules sin asignar hosts
- Usar
--hosts=allsin existir el hostgroup - No limpiar la caché de SSSD tras los cambios
Resultado
Los usuarios del grupo admins-linux pueden reiniciar NetworkManager como root y sin contraseña, con la política de sudo gestionada centralmente desde IdM.